by Chad Ostreicher | | Best Practices, IT infrastructure, IT Services, Security, Tips
Juice Jacking uses a charging station with malware loaded onto it by a hacker to gain unauthorized access to your device through its USB or micro-USB port. Generally speaking, this malware is a developing cybersecurity threat that mainly involves using the USB port to...
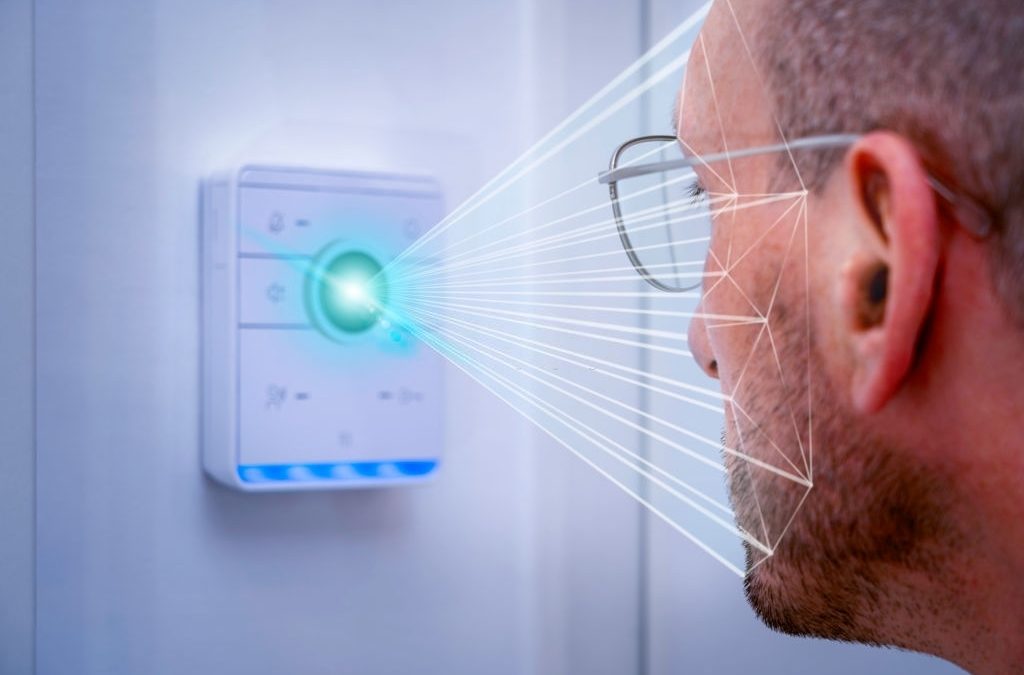
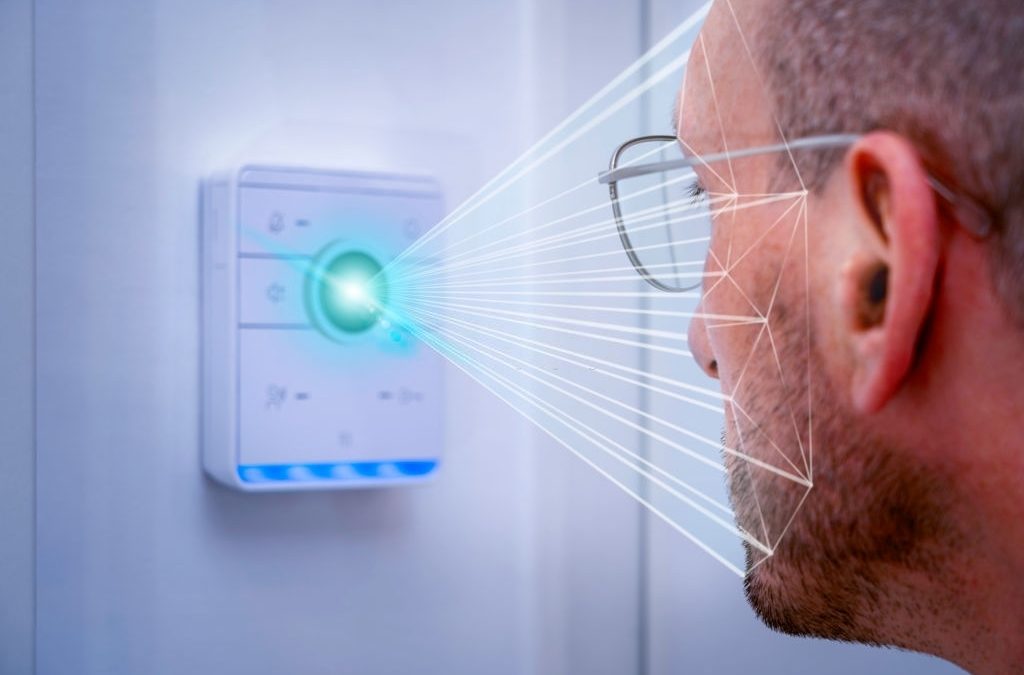
by Chad Ostreicher | | IoT, Security
Since the day that the smart doorbell arrived on an episode of Shark Tank, it’s been getting more and more popular among businesses, both large and small. Incredibly, you can visibly see someone ringing in and requesting access to your building, and what’s...

by Chad Ostreicher | | IT Services, Security
The fast development of technology and programming has brought many advantages and benefits for companies, institutions, and individuals. However, cyber threats have not lagged in terms of advancement and sophistication. Recently, we have seen how WannaCry, NotPetya,...

by Chad Ostreicher | | IT Services, Security
Working from home is the current daily routine for many. Unfortunately, the security of a home office is often less than stellar compared to in-office security. We could have come up with some boring basic cybersecurity tips, but we wanted to do something special. We...

by Chad Ostreicher | | Cloud Services, IT infrastructure, IT Services, Security, Tips, VoIP
As traditional telephone systems, which traditionally set up their connections via the copper cables of the fixed network, have been phased out, VoIP has opened up many new opportunities for telecommunications. However, some potential users are still unsure about this...