by Chad Ostreicher | | Cloud Services, IT Services, Security, Tips
DNS leak protection is incredibly important for businesses because DNS servers are the backbone of the Internet. DNS stands for Domain Name System, and it’s what converts letters into IP addresses so that you can connect to websites like Facebook or Google. DNS...

by Chad Ostreicher | | Cloud Services, IT infrastructure, IT Services, Security, Tips
There are many ways to move a business to the cloud, but many IT departments still don’t understand cloud migration strategies and basics. For example, many companies are offering the option of using Amazon Web Services for their cloud migration needs. However,...

by Chad Ostreicher | | IT Services, Security, Tips
As the cyber threats to business and personal computers continue to mount, in 2021, it will become more critical than ever for companies to implement cybersecurity measures to protect themselves from the increasing cybercrime risk. A recent study reveals that a...
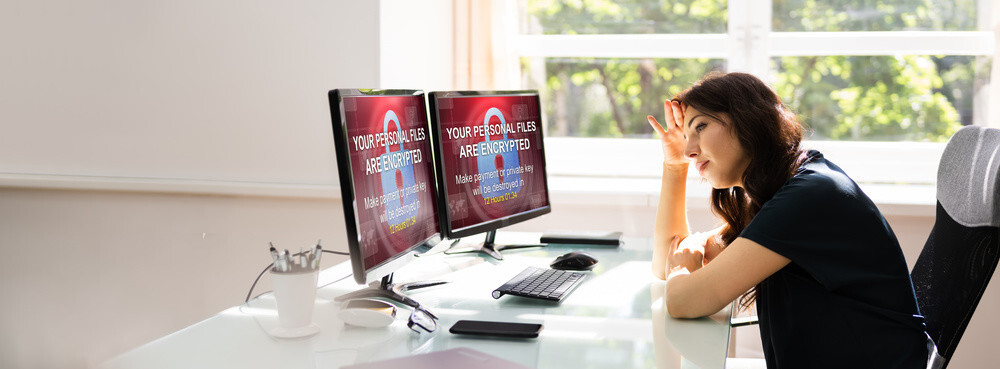
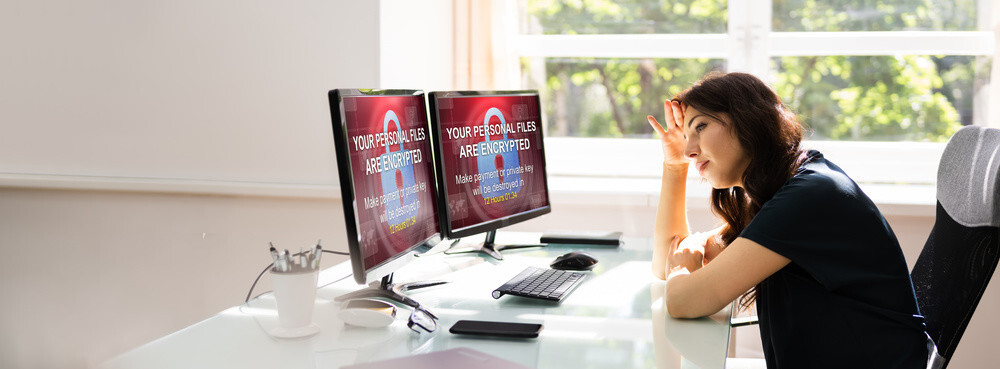
by Chad Ostreicher | | Ransomware, Security, Tips
There has been a lot of talk from us about ransomware lately, and this ransomware safety guide will be the only guide you need for 2021. We’ll go over everything from the basics, like what is ransomware? To something a bit more complex, why is it more successful...
by Chad Ostreicher | | Security
In the year 2019, millions of dollars and people were scammed during the holidays by scammers and hackers worldwide. While many people who were robbed during these times were American, the hackers and scammers often weren’t. They used a wide variety of tactics to...